January 30, 2014

Security Label 1
Today's rapidly changing economy, sophisticated counterfeiters and intensified worldwide competition make product packaging security more critical than ever. Brand owners, manufacturers and retailers place a premium on ensuring product authenticity and providing tamper-evidence.If a security program fails, the results can be lost sales and profits, inventory shrinkage, reduced brand equity, increased warranty repair costs, as well as consumer safety and liability issues.
The development of a valuable and effective packaging solution depends on discussing the four basic questions below with your security provider and end-use customer. The answers will help ensure effective protection of consumers, brand owners, and manufacturers for virtually every at-risk item on the market, from CDs to over-the-counter drugs to airplane parts.
1. What must be protected?
Identify the problem. Are products being diverted from the intended branch of the supply chain? Is the security device or label unreliable because of how it's applied? Are environmental conditions disabling the product's security measures? Do consumers send counterfeit products back for warranty repair? Fully understanding the threat will help determine the type of security devices required as well as the expected performance in use.
2. From whom must it be protected?
The selection of an effective security device depends heavily on the sophistication of those trying to defeat it. The complexity required to replicate or circumvent the device should be targeted at a level beyond the capabilities of the criminals in question. Consumers, street criminals, organized crime and emerging-nation manufacturers possess very different capabilities. Understanding who the perpetrators are will determine the level of security required and the number and type of devices and methods.
3. Who will police the system?
Even an optimal-security device can completely lose its value if no one verifies the system. Often, companies expect the consumer to police their security packaging. This approach fails when counterfeiters can produce a reasonable facsimile of the packaging that's good enough to fool the average consumer. Policing should take place at varying levels throughout the development, supply, distribution and retail chains. It can even take place when products are returned for warranty repair. Just as packaging must be more sophisticated than the criminals, inspectors and their inspection tools must also be at least as sophisticated as the security packaging.

Security Label 2
4. What is the cost of failure?Understanding the cost of security-system failure helps focus the development of the packaging on appropriate options.
Counterfeits resulting in lost profits and reduced brand equity carry a very different weight than those that result in personal injury or loss of life, as is possible with the counterfeiting of pharmaceuticals.
Sometimes a lack of a solid security program resulting in counterfeit goods on the market bears hidden costs as well. Consumers may file lawsuits against legitimate manufacturers for lack of appropriate counterfeit protection, resulting in added expense to the manufacturer. Understanding the overall cost and considerations of system failure can help ensure the development of an effective security system.
These questions must be discussed with the appropriate representatives of each company involved in the packaging development. If a security program lacks top-level support from the brand owner, it is crippled from the start. Designing a successful security program requires an understanding of the answers to the four questions above and a commitment of the entire supply chain to make it happen.
A security solution is a continuous program and not a onetime event.
P-s film for security, authenticity protection
Security, as it pertains to electronics and certain other products, generally centers on the protection of company profits and ensuring customer safety. Security requirements can be classified as overt, covert and forensic (traceability). A packaging security strategy in the overt sense might take the form of a label that is holographic in nature. For instance, the popular “Intel Inside” label found on some computers is a very visible confirmation of the product's authenticity, and it's designed so the consumer can clearly see it. If this security label is expected but isn't there, both the manufacturer and consumer lose.

Security Chart
Covert security

Security Chart
An example of a covert packaging security strategy can include the ability to have a label turn a certain color or otherwise change its appearance when it encounters a set of conditions that would knowingly cause the change. The actual label change can be undetectable to the human eye, but under the appropriate detection equipment, it becomes clear that the product is a counterfeit or has been damaged. This, then, gives the warranty provider and manufacturer legal grounds to void the warranty and reduce product life-cycle costs.
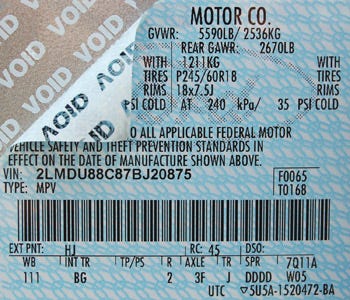
Traceability
The third example of product security is product traceability, which is part of the product manufacturer's forensic strategy. For example, an authenticated, unique label identifying each contract manufacturer can help a forensic analysis team in the event of a compromise in security. This allows the product manager or the owner to understand what happened and then evaluate or otherwise limit liability.
How can this data be stored on the product? An example of a mark that can be used is a 2D matrix code designed to pack a lot of information into a very small space. Some data-matrix symbols can store between one and 500 characters.
That means a data-matrix symbol has a maximum theoretical density of 500 million characters/in. Actual density will, of course, be limited by the resolution of the printing and reading technology used. With that much information available, the product traceability data can be stored on the label affixed to the product.
Choosing the right security method
In choosing the appropriate product packaging security method, manufacturers must factor in both the attributes of that method and the value of the product being protected.
The authenticity value of audio CDs and designer jeans may not be a big issue with consumers, but it's critical to the brand integrity of the provider.
On the other hand, electronic airplane parts are of crucial value to both the consumer and to the manufacturer. Choosing or developing the right p-s film label support and conveying the desired authenticity state is key to the early design and long-term security and profitability of a product.
Brand owners, retailers and manufacturers can increase their success by collaborating with a p-s film supplier and a label converter with substantial security application expertise.
You May Also Like