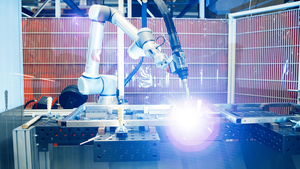
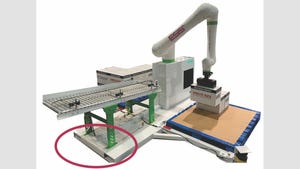
Automation
Machine Vision Packaging Inspection
Automation
A Vision of the Future: Machine Learning in Packaging InspectionA Vision of the Future: Machine Learning in Packaging Inspection
Today’s enhanced machine vision for packaging quality control definitely has its bright spots. But be wary of its shadows.
Sign up for the Packaging Digest News & Insights newsletter.